Web Architecture & Server Logic بنية الويب و منطق الخوادم
Modern Web Architecture has transitioned from traditional monolithic structures to Modular, Event-Driven frameworks. Logic is now distributed across Serverless Functions and Edge Runtimes to eliminate latency. انتقلت هندسة الويب الحديثة من الهياكل التقليدية إلى أطر عمل معيارية. يتم الآن توزيع المنطق عبر وظائف بدون خادم وتقنيات الحافة للقضاء تماماً على زمن التأخير.
Web Architecture & Server Logic بنية الويب و منطق الخوادم
Modern Web Architecture has transitioned from traditional monolithic structures to Modular, Event-Driven frameworks. Logic is now distributed across Serverless Functions and Edge Runtimes to eliminate latency. انتقلت هندسة الويب الحديثة من الهياكل التقليدية إلى أطر عمل معيارية. يتم الآن توزيع المنطق عبر وظائف بدون خادم وتقنيات الحافة للقضاء تماماً على زمن التأخير.
Foundational Infrastructure
البنية التحتية الأساسية
Pillars of Web Architecture & Server Login
أركان معمارية الويب ومنطق الدخول
Architecting resilient digital foundations and secure access layers to facilitate seamless data exchange and uncompromising system integrity.
هندسة قواعد رقمية مرنة وطبقات وصول آمنة لتسهيل تبادل البيانات بسلاسة وضمان سلامة الأنظمة عبر الشبكات العالمية.
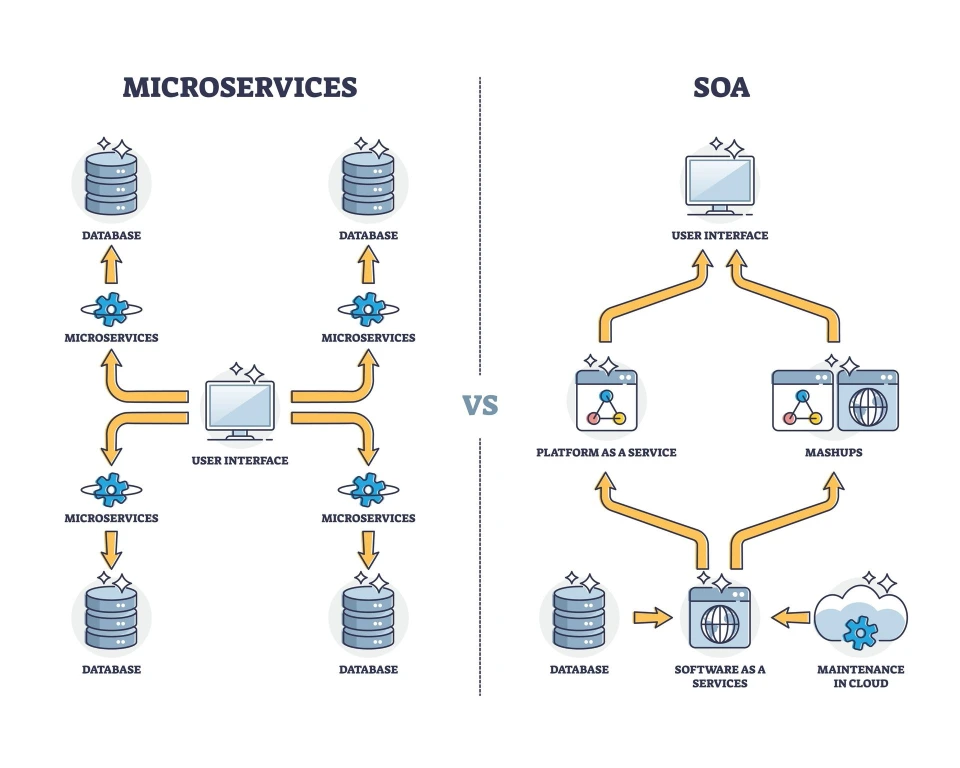
Distributed Microservices & API Orchestration
الخدمات المصغرة الموزعة وتنسيق API
Decoupling front-end layers from back-end logic to achieve granular scalability. This modular approach ensures components can be updated without risking total service outages.
فصل طبقات الواجهة الأمامية عن المنطق البرمجي الخلفي لتحقيق توسع دقيق. يضمن هذا النهج إمكانية تحديث المكونات دون المخاطرة بانقطاع الخدمة.
Unified Identity Management & Secure Authentication
إدارة الهوية الموحدة والمصادقة الآمنة
Sophisticated IAM systems utilizing MFA, SSO, and OAuth 2.0. These frameworks serve as the primary gateway for data protection across multiple server environments.
أنظمة IAM متطورة تستخدم MFA و SSO و OAuth 2.0. تعمل هذه الأطر كبوابة رئيسية لحماية البيانات عبر بيئات الخوادم المتعددة.
Edge Infrastructure & High-Availability Servers
بنية الحافة التحتية وخوادم التوافر العالي
Strategic placement of resources via CDNs and Edge Computing to minimize latency. Load balancing and automated failovers ensure zero-downtime continuity.
التوزيع الاستراتيجي للموارد عبر CDNs وحوسبة الحافة لتقليل التأخير. يضمن موازنة التحمل والنقل التلقائي للبيانات استمرارية الخدمة دون انقطاع.
Foundational Infrastructure
البنية التحتية الأساسية
Pillars of Web Architecture & Server Login
أركان معمارية الويب ومنطق الدخول
Architecting resilient digital foundations and secure access layers to facilitate seamless data exchange and uncompromising system integrity.
هندسة قواعد رقمية مرنة وطبقات وصول آمنة لتسهيل تبادل البيانات بسلاسة وضمان سلامة الأنظمة عبر الشبكات العالمية.
Distributed Microservices & API Orchestration
الخدمات المصغرة الموزعة وتنسيق API
Decoupling front-end layers from back-end logic to achieve granular scalability. This modular approach ensures components can be updated without risking total service outages.
فصل طبقات الواجهة الأمامية عن المنطق البرمجي الخلفي لتحقيق توسع دقيق. يضمن هذا النهج إمكانية تحديث المكونات دون المخاطرة بانقطاع الخدمة.
Unified Identity Management & Secure Authentication
إدارة الهوية الموحدة والمصادقة الآمنة
Sophisticated IAM systems utilizing MFA, SSO, and OAuth 2.0. These frameworks serve as the primary gateway for data protection across multiple server environments.
أنظمة IAM متطورة تستخدم MFA و SSO و OAuth 2.0. تعمل هذه الأطر كبوابة رئيسية لحماية البيانات عبر بيئات الخوادم المتعددة.
Edge Infrastructure & High-Availability Servers
بنية الحافة التحتية وخوادم التوافر العالي
Strategic placement of resources via CDNs and Edge Computing to minimize latency. Load balancing and automated failovers ensure zero-downtime continuity.
التوزيع الاستراتيجي للموارد عبر CDNs وحوسبة الحافة لتقليل التأخير. يضمن موازنة التحمل والنقل التلقائي للبيانات استمرارية الخدمة دون انقطاع.
Everything You Should Know About Web Architecture and Server Login
Web Architecture
Structured systems connect servers, data, and interfaces.
Server Infrastructure
Servers host apps and handle user requests efficiently.
Secure Server Access
Authentication systems protect servers and data access.
Layered Structure
Web systems are divided into logical functional layers.
Data Flow
Data moves between users, servers, and databases.
Client-Server Model
Browsers and servers communicate to deliver content.
هندسة الويب
أنظمة منظمة تربط الخوادم والبيانات والواجهات.
البنية التحتية للخوادم
تستضيف الخوادم التطبيقات وتتعامل مع طلبات المستخدمين بكفاءة.
الوصول الآمن إلى الخوادم
تحمي أنظمة المصادقة الوصول إلى الخوادم والبيانات.
البنية متعددة الطبقات
تنقسم أنظمة الويب إلى طبقات وظيفية منطقية.
تدفق البيانات
تنتقل البيانات بين المستخدمين والخوادم وقواعد البيانات.
نموذج العميل-الخادم
تتواصل المتصفحات والخوادم لتقديم المحتوى.
Web Architecture
Structured systems connect servers, data, and interfaces.
Server Infrastructure
Servers host apps and handle user requests efficiently.
Secure Server Access
Authentication systems protect servers and data access.
Layered Structure
Web systems are divided into logical functional layers.
Data Flow
Data moves between users, servers, and databases.
Client-Server Model
Browsers and servers communicate to deliver content.
هندسة الويب
أنظمة منظمة تربط الخوادم والبيانات والواجهات.
البنية التحتية للخوادم
تستضيف الخوادم التطبيقات وتتعامل مع طلبات المستخدمين بكفاءة.
الوصول الآمن إلى الخوادم
تحمي أنظمة المصادقة الوصول إلى الخوادم والبيانات.
البنية متعددة الطبقات
تنقسم أنظمة الويب إلى طبقات وظيفية منطقية.
تدفق البيانات
تنتقل البيانات بين المستخدمين والخوادم وقواعد البيانات.
نموذج العميل-الخادم
تتواصل المتصفحات والخوادم لتقديم المحتوى.
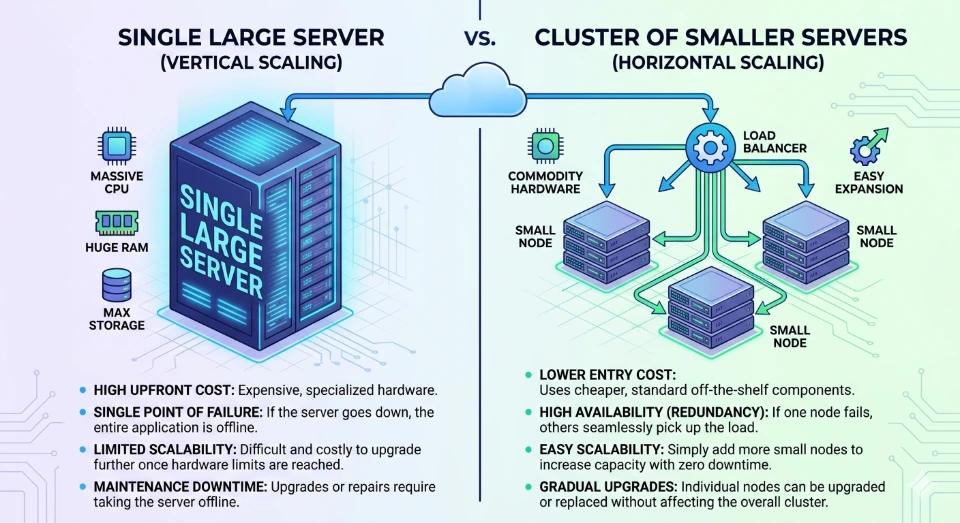
Scalability is the measure of a system’s ability to handle growing amounts of work. However, modern systems also require Elasticity—the ability to shrink resources during low-traffic periods to optimize costs. A truly scalable architecture isn't just about surviving a "Black Friday" surge; it’s about doing so without over-provisioning and wasting budget.
The Architecture of Growth
Vertical Scaling (The Limit): This involves adding more "muscle" (RAM or CPU) to a single machine. While simple to implement, it eventually hits a hardware ceiling and creates a single point of failure. If that one "super-server" goes down, the entire business halts.
Horizontal Scaling (The Future): This is the strategy of "Statelessness." By ensuring that no user data is tied to a specific server, we can deploy dozens or hundreds of identical, smaller instances. This allows for Auto-scaling, where the system automatically breathes—expanding when users arrive and contracting when they leave.
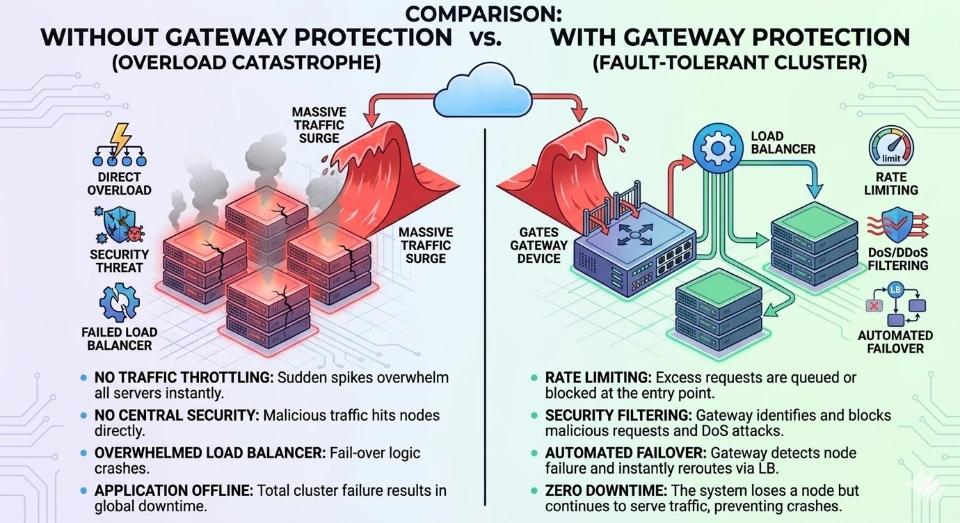
Reliability is the probability that a system will perform its intended function for a specified period. In professional web systems, this is measured in "Nines" (e.g., 99.9% uptime). Achieving this requires a "Design for Failure" approach, assuming that every component will eventually break.
Strategies for High Availability (HA)
Load Balancing & Health Checks: Sophisticated traffic managers don't just distribute requests; they perform constant "heartbeat" checks. If a server stops responding, it is instantly pulled from the rotation, and traffic is rerouted to healthy nodes.
Multi-Region Redundancy: True reliability means being "Geographic-Aware." By deploying across different physical data centers (Zones) or even different countries (Regions), the system can survive entire city-wide power outages or network failures.
Chaos Engineering: We don't wait for disasters to happen. By intentionally injecting failures into a staging environment, we ensure the system's automated recovery protocols work exactly as intended.
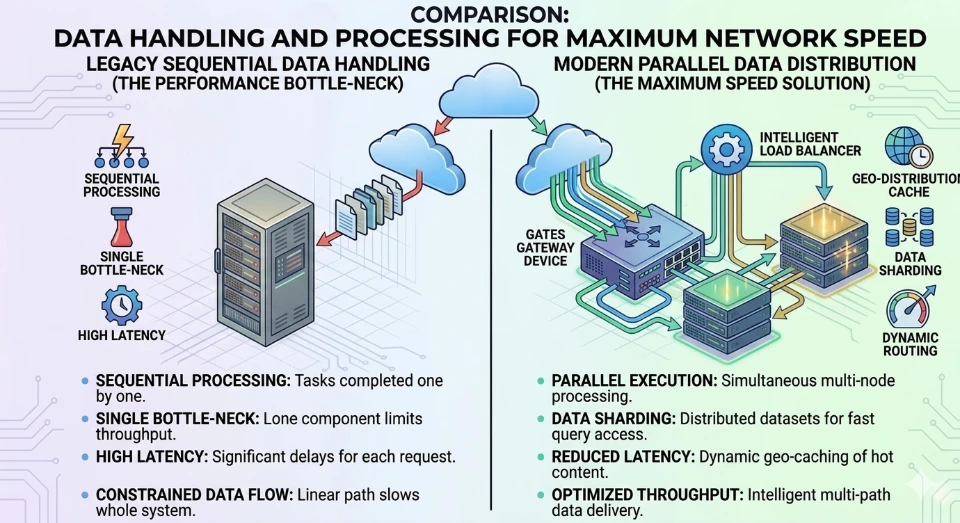
As a system grows, the database is almost always the first component to struggle. Unlike web servers, databases carry "state" (data), making them harder to replicate. We solve this by applying the CAP Theorem (Consistency, Availability, and Partition Tolerance) to choose the right tool for the job.
Advanced Data Strategies
Read/Write Segregation: Most web applications are "read-heavy." By using Read Replicas, we direct 90% of the traffic (browsing, searching) to secondary copies of the data, leaving the primary database dedicated solely to critical "write" operations (purchases, updates).
Database Sharding: When a dataset becomes too massive for one machine, we "shard" it—splitting it into horizontal slices. For example, users A-M live on one database, while N-Z live on another. This distributes the heavy I/O load across multiple hardware units.
Caching with Redis/Memcached: The fastest database query is the one you never have to make. By storing frequently accessed data in high-speed RAM, we can reduce response times from milliseconds to microseconds.
The "Monolith" (one giant codebase) is a liability for growing companies. If one small feature crashes, the whole site goes down. Modern systems use Microservices and Containerization to isolate features into independent, manageable units.
The Modular Advantage
Containerization (Docker & Kubernetes): We package code and its entire environment into a "Container." This ensures that if it works on a developer's machine, it will work exactly the same way in the cloud, eliminating "environment drift."
Event-Driven Architecture: Instead of services talking directly to each other (which creates dependencies), they communicate via a Message Broker (like RabbitMQ or Kafka). If the "Email Service" is down, the "Order Service" still works; it simply drops a message in the queue for the email service to pick up once it restarts.
Technology Diversity: Microservices allow us to use the right language for the right task—perhaps Python for AI tasks, Node.js for real-time chats, and .NET or Go for high-performance financial logic.
Reliability is also about perceived performance. A system that takes 10 seconds to load is "down" in the eyes of the user. To reach a global audience, we must fight the physics of distance.
Optimizing the User Experience
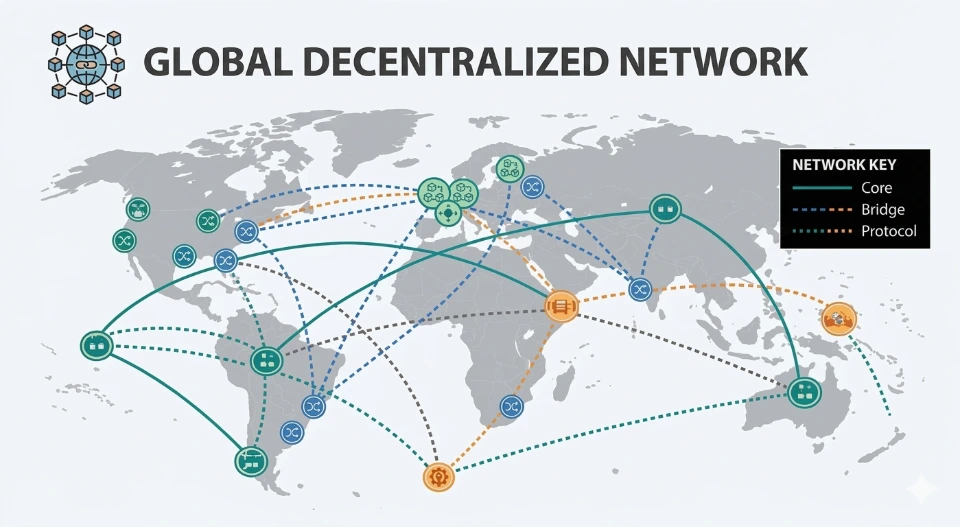
Content Delivery Networks (CDN): By caching images, videos, and scripts on "Edge" servers located in cities around the world, we ensure that a user in London doesn't have to wait for a server in New York to respond.
Edge Computing: Beyond just images, we now run logic "at the edge." This allows for instant tasks—like authentication or header manipulation—to happen hundreds of miles closer to the user, drastically reducing Time to First Byte (TTFB).
Static Site Generation (SSG): For high-traffic pages, we pre-render the entire site into static HTML. Serving a file is significantly faster and more reliable than generating a page from a database every time someone clicks.
Scalability & Resilience
التوسع والمرونة
Infrastructure Autonomy & Elasticity
استقلالية ومرونة البنية التحتية
The evolution from static hosting to autonomous infrastructure represents a fundamental shift. Automation is now a requirement for high-traffic platforms where self-healing architectures and containerized environments ensure digital foundations solve problems independently.
يمثل التطور من الاستضافة الثابتة إلى البنية التحتية المستقلة تحولاً جذرياً. الأتمتة الآن ضرورة للمنصات عالية الكثافة، حيث تضمن بنيات الإصلاح الذاتي وبيئات الحاويات حل المشكلات بشكل مستقل.
This is best observed in elastic scaling. Unlike traditional setups, modern architecture uses intelligent load balancing to monitor health and deploy additional instances in seconds during surges, optimizing costs automatically once demand subsides.
يتجلى هذا بوضوح في التوسع المرن. على عكس الإعدادات التقليدية، تستخدم المعمارية الحديثة موازنة تحميل ذكية لمراقبة الحالة ونشر خوادم إضافية في ثوانٍ أثناء الضغط، مع تحسين التكاليف تلقائياً عند انخفاض الطلب.

Scalability & Resilience
التوسع والمرونة
Infrastructure Autonomy & Elasticity
استقلالية ومرونة البنية التحتية
The evolution from static hosting to autonomous infrastructure represents a fundamental shift. Automation is now a requirement for high-traffic platforms where self-healing architectures and containerized environments ensure digital foundations solve problems independently.
يمثل التطور من الاستضافة الثابتة إلى البنية التحتية المستقلة تحولاً جذرياً. الأتمتة الآن ضرورة للمنصات عالية الكثافة، حيث تضمن بنيات الإصلاح الذاتي وبيئات الحاويات حل المشكلات بشكل مستقل.
This is best observed in elastic scaling. Unlike traditional setups, modern architecture uses intelligent load balancing to monitor health and deploy additional instances in seconds during surges, optimizing costs automatically once demand subsides.
يتجلى هذا بوضوح في التوسع المرن. على عكس الإعدادات التقليدية، تستخدم المعمارية الحديثة موازنة تحميل ذكية لمراقبة الحالة ونشر خوادم إضافية في ثوانٍ أثناء الضغط، مع تحسين التكاليف تلقائياً عند انخفاض الطلب.


Identity & Governance
الهوية والحوكمة
Adaptive Access and Identity Governance
الوصول التكيفي وحوكمة الهوية
Server login and identity management have transitioned from simple gatekeeping to sophisticated, context-aware security. By moving away from static credentials toward automated governance, we create a "zero-trust" environment where access is continuously verified based on behavior, location, and device health.
لقد انتقلت إدارة الدخول إلى الخوادم وإدارة الهوية من مجرد حراسة بسيطة إلى أمن متطور يدرك السياق. من خلال الابتعاد عن بيانات الاعتماد الثابتة نحو الحوكمة المؤتمتة، ننشئ بيئة "ثقة صفرية" حيث يتم التحقق من الوصول باستمرار بناءً على السلوك والموقع وسلامة الجهاز.
Modern systems analyze variables in real-time. If an administrator attempts access from an unrecognized location, the system triggers automated scrutiny—effectively balancing airtight security with operational speed to ensure the server remains impenetrable.
تحلل الأنظمة الحديثة المتغيرات في الوقت الفعلي. إذا حاول مسؤول الوصول من موقع غير معترف به، فإن النظام يطلق تدقيقاً مؤتمتاً، مما يوازن بفعالية بين الأمن المحكم والسرعة التشغيلية لضمان بقاء الخادم منيعاً.

Identity & Governance
الهوية والحوكمة
Adaptive Access and Identity Governance
الوصول التكيفي وحوكمة الهوية
Server login and identity management have transitioned from simple gatekeeping to sophisticated, context-aware security. By moving away from static credentials toward automated governance, we create a "zero-trust" environment where access is continuously verified based on behavior, location, and device health.
لقد انتقلت إدارة الدخول إلى الخوادم وإدارة الهوية من مجرد حراسة بسيطة إلى أمن متطور يدرك السياق. من خلال الابتعاد عن بيانات الاعتماد الثابتة نحو الحوكمة المؤتمتة، ننشئ بيئة "ثقة صفرية" حيث يتم التحقق من الوصول باستمرار بناءً على السلوك والموقع وسلامة الجهاز.
Modern systems analyze variables in real-time. If an administrator attempts access from an unrecognized location, the system triggers automated scrutiny—effectively balancing airtight security with operational speed to ensure the server remains impenetrable.
تحلل الأنظمة الحديثة المتغيرات في الوقت الفعلي. إذا حاول مسؤول الوصول من موقع غير معترف به، فإن النظام يطلق تدقيقاً مؤتمتاً، مما يوازن بفعالية بين الأمن المحكم والسرعة التشغيلية لضمان بقاء الخادم منيعاً.
What We Can Do For You
Performance Optimization is the process of improving a system's speed, responsiveness, and efficiency. In web development and ERP management, this involves minimizing resource consumption (like CPU or memory) while maximizing the speed at which tasks are completed or pages are loaded.
Performance Optimization is the process of improving a system's speed, responsiveness, and efficiency. In web development and ERP management, this involves minimizing resource consumption (like CPU or memory) while maximizing the speed at which tasks are completed or pages are loaded.
Automated Data Protection refers to the use of software and pre-defined policies to handle security tasks without manual intervention. By removing the risk of human error, these systems ensure that backups, encryption, and threat responses happen consistently and instantly.
Secure Server Access refers to the protocols and technologies used to ensure that only authorized individuals can connect to and manage a server. It moves away from simple passwords—which are easily stolen or guessed—toward multi-layered authentication and encrypted communication.
Access Control Management (ACM) is the framework of policies and technologies used to ensure that the right people have access to the right data at the right time—and for the right reasons. It is the digital equivalent of a security guard checking IDs and cross-referencing them with a guest list before allowing entry to specific rooms in a building.
Advanced Security Systems in 2026 represent a shift from reactive tools to predictive, autonomous ecosystems. These systems no longer just alert you when a door is opened or a file is accessed; they use artificial intelligence to anticipate threats and automatically adjust defenses in real-time.

Let's Connect Today!
My Company
- Garhoud Views Building – 7th Floor -Office 711-01 Dubai UAE
- +971509862203
- +971509862239
- info@itdtech.ae


